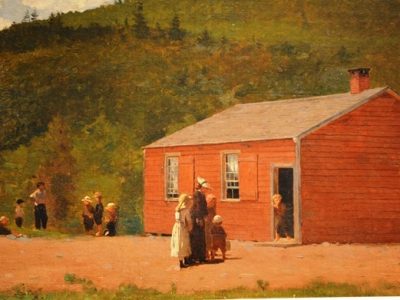
There is a National Girls Collaborate Project I actually loved math, can you imagine? My father, the doctor, thought it was ill advised to pursue my studies in mathematics; I think he may have changed his mind. It is never too early to introduce and encourage girls to not only study, but to enjoy, science,…